Wiring Trust Into Every Room
Mapping the Core: Topology Choices That Endure

Cables, Radios, and Backhaul That Just Work
Segmentation, Addressing, and Quality of Service
VLANs That Keep Curiosity Contained
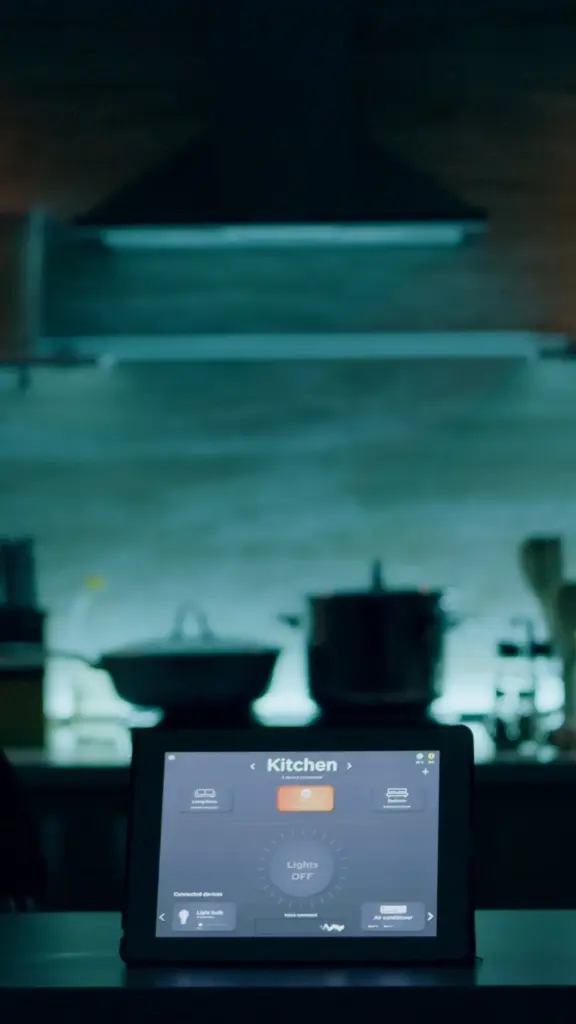
Group consumer IoT, household devices, guests, and management interfaces into distinct VLANs with clear, documented firewall rules. Block lateral movement by default, then open precise ports for discovery, updates, or controller access. Use mDNS reflectors or proxies only where necessary. Minimizing privileges limits surprises from experimental firmware, cloud outages, or odd vendor behavior. Your lights can still glow warmly while your data remains serenely private.
IP Planning Without Renumbering Nightmares
Pick subnets with growth headroom and logical ranges per floor or zone. Reserve addresses for controllers, cameras, bridges, and critical infrastructure. Use DHCP reservations for predictability, and descriptive hostnames for sanity. Keep a simple, living map of your allocations, including notes on VLAN tags and switch ports. Thoughtful planning prevents disruptive renumbering later, protecting weekends and preserving goodwill when relatives ask for streaming help during dinner.
QoS That Protects the Moment
Prioritize what matters: doorbell video, voice assistants, and teleconferences conflict less when marked correctly and shaped at the gateway. Configure DSCP on trusted gear, verify queues on switches, and avoid overcomplication. Test with iperf, real calls, and doorbell presses. The goal is small, meaningful guarantees, not fragile complexity. When someone rings, greets, and enters, the network should feel invisible and perfectly courteous.
Resilience and Redundancy at Home Scale

Security Without Breaking Convenience



Observability, Maintenance, and Growth
Measure Before You Worry
Updates Without Regret
Future-Proofing Gracefully
All Rights Reserved.